📋 Project Overview
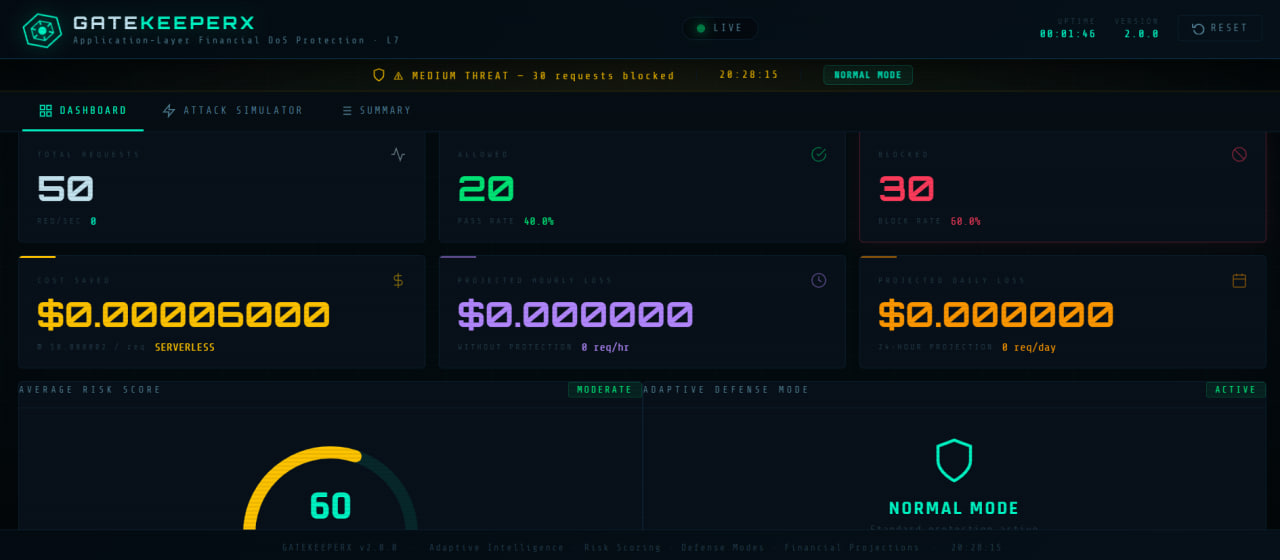
GateKeeperX is a production-grade Web Application Firewall (WAF) that acts as a reverse proxy, sitting between clients and backend applications. It intercepts all incoming traffic and applies intelligent rate limiting, IP blocking, and adaptive defense escalation to shield the backend from Layer 7 DDoS attacks.
Built for a hackathon, GateKeeperX goes beyond basic rate limiting — it includes a real-time dashboard, a risk scoring engine, financial impact tracking, and an escalating defense system that automatically tightens restrictions as attacks intensify.
🏗️ Architecture
All client requests hit GateKeeperX first. Allowed traffic is forwarded to the protected backend; blocked traffic is rejected with a 429 response. All activity streams to the live dashboard.
🔁 How It Works
- Client Request — GateKeeperX intercepts all incoming traffic
- Security Check — Rate limiting, risk scoring, and IP blocking are evaluated
- Forward — If allowed, the request is proxied to the protected backend
- Response — The backend response is returned to the client with WAF headers
- Logging — All activity is logged and streamed to the real-time dashboard
⚡ Key Features
- Real reverse proxy — full transparent traffic interception and forwarding
- Adaptive defense system — three escalating modes triggered automatically by attack volume
- Risk scoring engine — 0–100 score based on burst intensity, repeat offenses, and rate acceleration
- Exponential IP blocking — durations escalate per offender: 60s → 90s → 135s → max 600s
- Financial impact analytics — real-time cost savings, hourly/daily projections, and ROI metrics
- Live dashboard — requests/sec chart, blocked IPs, threat level indicator, top attackers list
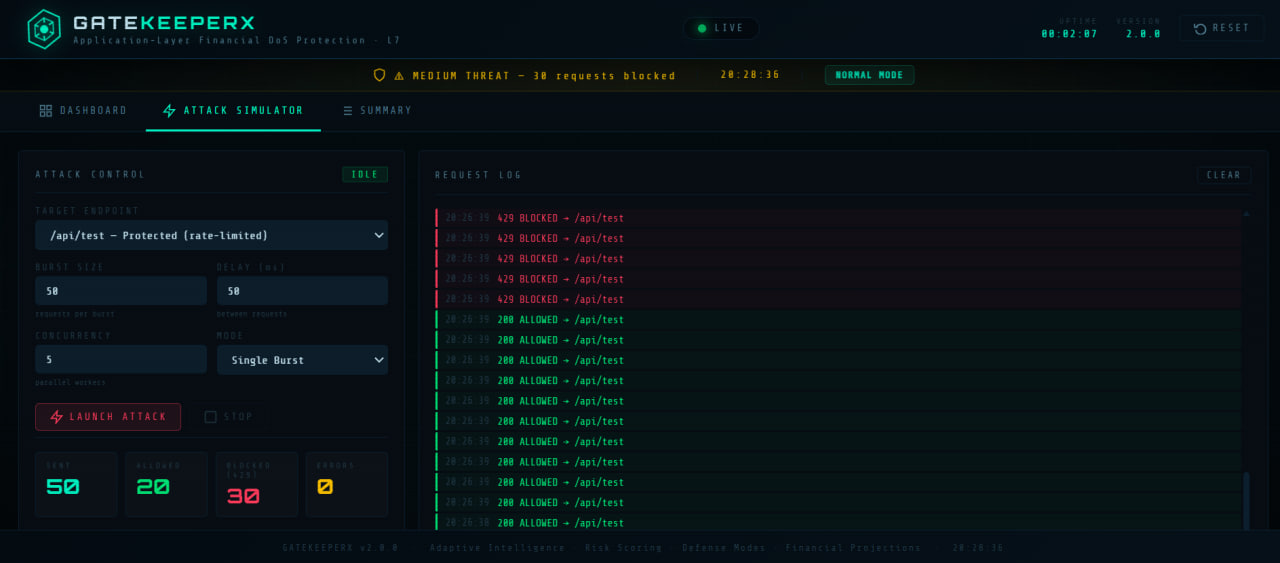
- Built-in attack simulator — demo script to trigger rate limits and watch defense escalation live
🛡️ Adaptive Defense Modes
| Mode | Trigger | Request Limit | Block Time |
|---|---|---|---|
| NORMAL | Default | 20 req / 5s | 60s |
| ELEVATED | 30 IPs blocked | 15 req / 5s | 120s |
| DEFENSE | 100 IPs blocked | 10 req / 5s | 300s |
💾 Code Sample — Rate Limiter Core
from collections import defaultdict, deque
import time
class RateLimiter:
def __init__(self):
self.request_windows = defaultdict(deque)
self.blocked_ips = {}
self.block_counts = defaultdict(int)
self.defense_mode = "NORMAL"
self.blocked_total = 0
self.MODE_LIMITS = {
"NORMAL": {"requests": 20, "window": 5, "block_time": 60},
"ELEVATED": {"requests": 15, "window": 5, "block_time": 120},
"DEFENSE": {"requests": 10, "window": 5, "block_time": 300},
}
def is_allowed(self, ip: str) -> dict:
now = time.time()
# Check active block
if ip in self.blocked_ips:
if now < self.blocked_ips[ip]:
return {"allowed": False, "reason": "IP_BLOCKED"}
del self.blocked_ips[ip]
limits = self.MODE_LIMITS[self.defense_mode]
window = self.request_windows[ip]
# Slide time window
while window and now - window[0] > limits["window"]:
window.popleft()
if len(window) >= limits["requests"]:
self._block_ip(ip, limits["block_time"])
self.blocked_total += 1
self._escalate_defense()
return {"allowed": False, "reason": "RATE_LIMIT_EXCEEDED"}
window.append(now)
return {"allowed": True}
def _block_ip(self, ip: str, base_time: int):
"""Exponential backoff per repeat offender."""
count = self.block_counts[ip]
duration = min(base_time * (1.5 ** count), 600)
self.blocked_ips[ip] = time.time() + duration
self.block_counts[ip] += 1
def _escalate_defense(self):
"""Auto-escalate defense mode by total blocks."""
if self.blocked_total >= 100:
self.defense_mode = "DEFENSE"
elif self.blocked_total >= 30:
self.defense_mode = "ELEVATED"▶ Quick Start
# Clone and setup
git clone https://github.com/raoufats26/GateKeeperX
cd GateKeeperX
python3 -m venv venv && source venv/bin/activate
pip install fastapi uvicorn httpx requests
# Terminal 1 — start protected backend
python3 protected_server/app.py
# Terminal 2 — start GateKeeperX WAF
uvicorn backend.main:app --host 127.0.0.1 --port 8000 --reload
# Test normal traffic
curl http://127.0.0.1:8000/proxy/data
# X-GateKeeperX: Protected
# X-Protected-By: GateKeeperX-WAF-v2.0
# Simulate an attack — watch the dashboard escalate
python3 attacker/attack.py📡 API Endpoints
| Endpoint | Method | Description |
|---|---|---|
| / | GET | Live dashboard |
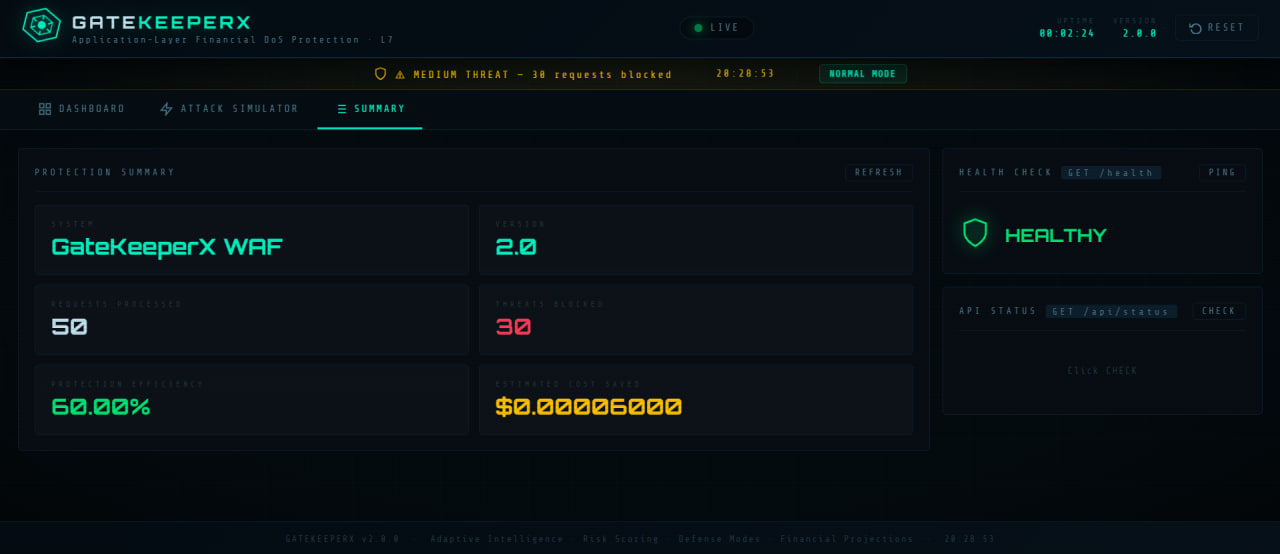
| /health | GET | WAF health check |
| /proxy/{path} | ALL | Reverse proxy to backend |
| /api/metrics | GET | Real-time metrics JSON |
| /api/summary | GET | Protection summary |
| /api/reset | POST | Reset all metrics |
📸 Screenshots